What is OSI Reference Model?
The Open Systems Interconnection (OSI) reference model or just OSI model helps you understand how data in a networking environment actually works from one computer to another, regardless of where the computer is or what software it runs.
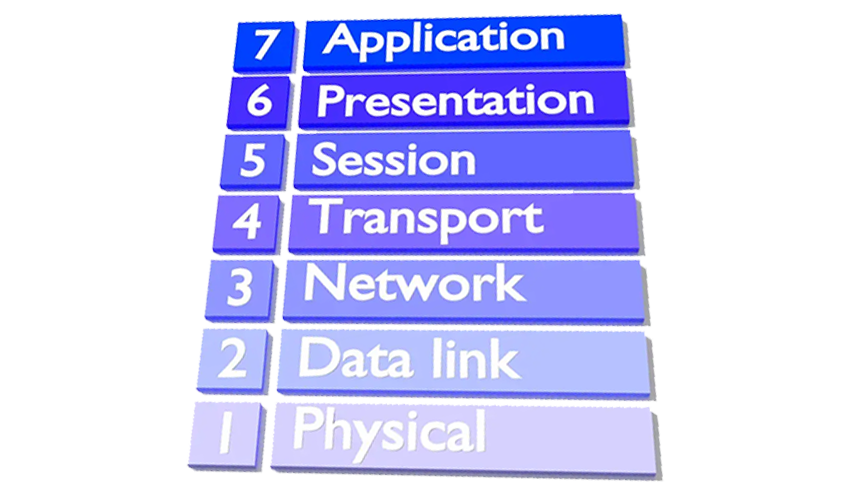
This model is composed of seven layers, with each corresponding devices, protocols, standards, and applications in the real world.
Computer network specialists use the OSI model to aid them when designing, maintaining, and troubleshooting their networks.
This article defines each of the OSI model layers, how they work and associated protocols and applications
Why was the OSI Model Created?
The OSI model was created and ratified by the International Organization for Standardization (ISO), and it is represented in the United States by the American National Standards Institute (ANSI). This model was created to do the following:
- Explain network communications between hosts on a LAN or WAN.
- Present a categorization system for communication protocol suites.
- Show how different protocol suites can communicate with each other
The OSI model was created as a set of seven layers each of which houses different protocols within one of several protocol suites, the most common of which is TCP/IP.
The OSI model shows how a protocol stack works on different levels of transmission (that is, how it stacks up against the model). As mentioned previously, a LAN requires computers with network adapters. These must be connected together in some way to facilitate the transfer of data.
Seven layers of the OSI Model
Layer 1—Physical layer
This is the physical and electrical medium for data transfer. It includes but is not limited to cables, jacks, patch panels and hubs. Concepts related to the physical layer include topologies, analog versus digital/encoding, bit synchronization, baseband versus broadband, multiplexing, and serial (5-volt logic) data transfer. If you can touch a network element, it is part of the physical layer, which makes this layer one of the easiest to understand.
The unit of measurement used on this layer is bits.
Layer 2—Data link layer (DLL)
This layer establishes, maintains, and decides how transfer is accomplished over the physical layer. Devices that exist on the DLL are network interface cards and bridges. This layer also ensures error free transmission over the physical layer under LAN transmissions. It does so through physical addresses (the hexadecimal address that is burned into the ROM of the NIC), otherwise known as the MAC address.
The unit of measurement used on this layer is frames.
Layer 3—Network layer
This layer is dedicated to routing and switching information to different networks, LANs, or internetworks. Devices that exist on the network layer are routers and IP switches. Here, we are getting into the logical addressing of hosts. Instead of physical addresses, the addressing system of the computer is stored in the operating system—for example, IP addresses.
Now you can see that a typical computer will really have two addresses: a physical or hardware-based address such as a MAC address, and a logical or software-based address such as an IP address. Part of the trick in networking is to make sure the two addresses get along together.
A layer 3 switch differs from a layer 2 switch in that it determines paths for data using logical addressing (IP addresses) instead of physical addressing (MAC addresses
The unit of measurement used on this layer is packets
Layer 4—Transport layer
This layer ensures error-free transmission between hosts through logical addressing. Therefore, it manages the transmission of messages through layers 1 through 3. The protocols that are categorized by this layer break up messages, send them through the subnet, and ensure correct reassembly at the receiving end, making sure there are no duplicates or lost messages. This layer contains both connection-oriented and connectionless systems. Inbound and outbound ports are controlled by this layer. When you think “ports,” think the transport layer.
Two common TCP/IP protocols that are utilized on this layer include the Transmission Control Protocol (TCP), which is a connection-oriented protocol, and the User Datagram Protocol (UDP), which is connectionless.
An example of an application that uses TCP is a web browser, and an example of an application that uses UDP is streaming media.
When you download a web page, you don’t want to lose any packets of information because graphics would appear broken, certain text wouldn’t read correctly, and so on. By using TCP, we ensure that data gets to its final destination. If a packet is lost along the way, it will be resent until the destination computer acknowledges delivery or ends the session. But with streaming media, we are either watching or listening in real time. So, if a packet is lost, we don’t really care, because that time frame of the video or music has already passed.
The unit of measurement used on this layer is sometimes referred to as segments or messages.
Layer 5—Session layer
This layer governs the establishment, termination, and synchronization of sessions within the Operating System over the network and between hosts—for example, when you log on and log off. This is the layer that controls the name and address database for the OS or NOS. NetBIOS (Network Basic Input Output System) works on this layer.
Layer 6—Presentation layer
This layer translates the data format from sender to receiver in the various OSes that may be used. Concepts include code conversion, data compression, and file encryption. Redirectors work on this layer, such as mapped network drives that enable a computer to access file shares on a remote computer.
Layer 7—Application layer
This layer is where message creation—and, therefore packet creation—begins. DB access is on this level. End-user protocols such as FTP, SMTP, Telnet, and RAS work at this layer. For example, suppose you are using Outlook Express. You type a message and click Send. This initiates SMTP (Simple Mail Transfer Protocol) and other protocols, which send the mail message down through the other layers, breaking it into packets at the network layer and so on. This layer is not the application itself, but the protocols that are initiated by this layer.
Reviewing the OSI Layers
Although earlier in the lesson, we defined each of the OSI layers starting at the bottom, the physical layer, and moving upward from there, quite often, you will see the layers listed from the top down, with the application layer at the top and the physical layer at the bottom, as shown in Figure below

In general, data transactions start at the sending computer, travel down the OSI layers starting with the application layer and ending with the physical layer, are transmitted across the physical medium be it wired or wireless, and travel back up the layers of the OSI model at the receiving computer.
For example, if you wanted to connect to a Web site, you would type the name of the site in your web browser’s address field. Then, when you press Enter, the HTTP protocol would take effect at the application layer. The packets of data would be compressed (with gzip) and possibly encrypted (HTTPS by way of SSL or TLS) at the presentation layer. The web server would acknowledge the session with the client web browser at the session layer.
The information would then be transmitted as TCP information on the transport layer, where ports are also selected. The TCP information would be broken up into easy-to-send packets on the network layer, and IP addressing information would be added. The packets would then be sent to the data link layer, where the network adapter would encapsulate them into frames of data. Then, at the physical layer, the network adapter would break the frames up into a serial bit stream to be sent over the cable media.
The figure below reviews the OSI layers and shows the corresponding devices, protocols, and network standards that apply to each layer.

Defining the TCP/IP Model
TCP/IP (Transmission Control Protocol/ Internet Protocol) are a set of standard rules that allows different types of computers to communicate with each other. The IP protocol ensures that each computer that is connected to the Internet is having a specific serial number called the IP address.
The TCP/IP model is similar to the OSI model. It is often used by software manufacturers who are not as concerned with how information is sent over physical media, or how the data link is actually made.
Although the OSI model is a reference model, the TCP/IP model (also known as Internet model) is more descriptive, defining principles such as “end-to-end” and “robustness,” which describe strong endpoint connections and conservative transmission of data.
The four layers in the TCP/IP model are as follows:
- Application Layer: The application layer makes sure that the data from the sending end is received in a format that is acceptable and supported at the receiving end.
- Transport Layer: The transport layer is responsible for the smooth transmission of data from one end to the other. It is also responsible for reliable connectivity, error recovery, and flow control of the data.
- Internet Layer: This Internet Layer moves packets from source to destination by connecting independent networks.
- Network Access Layer: The Network Access Layer sees how a computer connects to a network.
The OSI physical layer is skipped altogether, and the application layer comprises the OSI application, presentation, and session layers.
Programmers utilize the TCP/IP model more often than the OSI model, whereas network administrators usually benefit to a higher degree from the OSI model. Programmers are generally interested in the interfaces made to the application and transport layers. Anything below the transport layer is taken care of by the TCP/IP stack within the operating system, which is set in stone. Programs can be made to utilize the TCP stack, but not to modify it.