Introduction
The Internet is an increasingly important part of everyday life for people around the world and keeps on defining how people co-exists with each other. But if you’ve never used the Internet before, all of this new information might feel a bit confusing at first. This is the 6th lesson in my YouTube Channel series where I am teaching about Internet and Web fundamentals. In this article, we are going to look at Understanding Internet Basics and Virtual Private Networks (VPN). You can also look at Routing and Switching as part of Wide Area Network
What is the Internet?
The Internet is a worldwide system of connected computer networks. Computers that connect to the Internet use the TCP/IP protocol suite.In our previous article, we learnt that TCP/IP are a set of standard rules that allows different types of computers to communicate with each other over the internet.

With the Internet, it’s possible to access almost any information, communicate with anyone else in the world, and do much more.
The origins of the Internet can be traced back to ARPANET, which was developed by the U.S. government for security purposes; however, ARPANET (Advanced Research Projects Agency Network) was a disjointed group of networks using outmoded or non-uniform protocols. By using TCP/IP to join different types of networks together, the Internet was created.
History of internet
On October 29, 1969, an organization called ARPANET (Advanced Research Projects Agency) launched the first iteration of the internet (also known as ARPANET) connecting four major computers at The University of Utah, UCSB (University of California, Santa Barbara), UCLA (University of California, Los Angeles), and Stanford Research Institute.
When this network of computers was connected, universities were able to access files and transmit information from one organization to the other, as well as internally.
As researchers developed the system, they continued to connect computers from other universities, including MIT and Harvard. Eventually, ARPANET was renamed “internet.”
TCP/IP (Transmission Control Protocol and Internet Protocol) was established in the 1970s, allowing internet technology to mature. The development of these protocols aided in the standardization of how data was sent and received via the internet.
As a result, the internet has been able to diversify and grow swiftly. Wi-Fi was first introduced in 1997. The year is 1998, and Windows 98 is released. Smartphone use is widespread in 2007. The 4G network is launched in 2009.
The internet is used by 3 billion people nowadays. By 2030, there are expected to be 7.5 billion internet users and 500 billion devices linked to the internet.
How does internet works
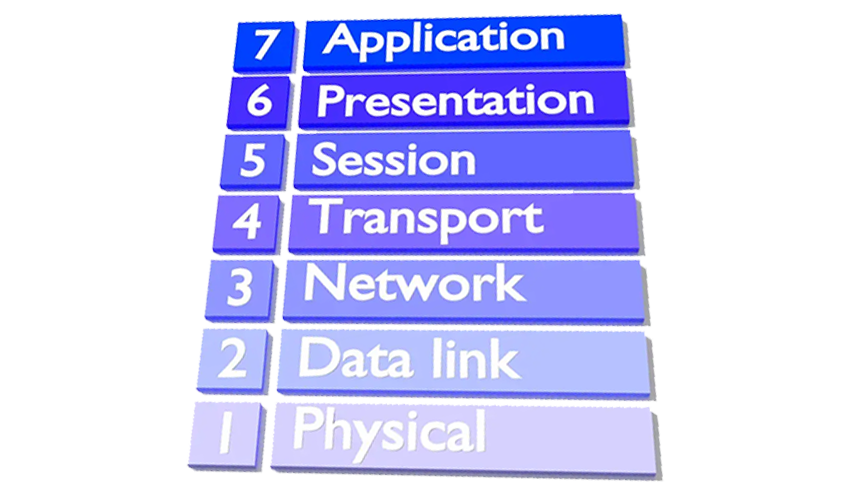
We have learnt that internet is a worldwide computer network that transmits a variety of data and media across interconnected devices. It works by using a packet routing network that follows Internet Protocol (IP) and Transport Control Protocol (TCP) which we looked in the previous chapters.
TCP and IP work together to ensure that data transmission across the internet is consistent and reliable, no matter which device you’re using or where you’re using it.
When data is transferred over the internet, it’s delivered in messages and packets. Data sent over the internet is called a message, but before messages get sent, they’re broken up into tinier parts called packets.
These messages and packets travel from one source to the next using Internet Protocol (IP) and Transport Control Protocol (TCP). IP is a system of rules that govern how information is sent from one computer to another computer over an internet connection.
Using a numerical address (IP Address) the IP system receives further instructions on how the data should be transferred.
The Transport Control Protocol (TCP) works with IP to ensure transfer of data is dependable and reliable. This helps to make sure that no packets are lost, packets are reassembled in proper sequence, and there’s no delay negatively affecting the data quality.
Example, when you type a web address in a browser…
Your PC or device is connected to the web through a modem or router. Together, these devices allow you to connect to other networks around the globe. Your router enables multiple computers to join the same network while a modem connects to your ISP (Internet Service Provider) which provides you with either cable or DSL internet.
- Step 1: Type in a web address, known as a URL (Uniform Resource Locator) e.g. www.google.com. Each website has its own unique URL that signals to your ISP where you want to go.
- Step 2: Your query is pushed to your ISP which connects to several servers which store and send data like a DNS (Domain Name Server).
- Step 3: Next, your browser looks up the IP address for the domain name you typed into your search engine through DNS. DNS then translates the text-based domain name you type into the browser into the number-based IP address.
Example: Google.com becomes 64.233.191.255 - Step 4: Your browser sends a Hypertext Transfer Protocol (HTTP) request to the target server to send a copy of the website to the client using TCP/IP.
- Step 5: The server then approves request and sends a “200 OK” message to your computer. Then, the server sends website files to the browser in the form of data packets. As your browser reassembles the data packets, the website loads allowing you to learn, shop, browse, and engage.
Uses of the Internet
- E-mail: E-mail is an electronic message sent across a network from one computer user to one or more recipients. It refers to the internet services in which messages are sent from and received by servers.
- Web Chat: Web chat is an application that allows you to send and receive messages in real-time with others. By using Internet chat software, the user can log on to specific websites and talk with a variety of other users online. Chat software is interactive software that allows users to enter comments in one window and receive responses from others who are using the same software in another window.
- World Wide Web: The World Wide Web is the Internet’s most popular information exchange service. It provides users with access to a large number of documents that are linked together using hypertext or hyperlinks. We will cover more about the world wide web in the next topic
- Internet telephony: The technique that converts analog speech impulses into digital signals and routes them through packet-switched networks of the internet is known as internet telephony.
- Video conferencing: This refers to the use of voice and images to communicate amongst users.
Defining Intranets and Extranets
Intranets and extranets are used by organizations to share data with select individuals. Whereas an intranet is used by an organization to share data with its employees, an extranet is used to share data with sister companies or other partnered organizations.
- An intranet is a private computer network or single Web site that an organization implements in order to share data with employees around the world. User authentication is necessary before a person can access the information in an intranet; ideally, this keeps the general public out, as long as the intranet is properly secured.Generally, a company refers to its intranet as its private Web site, or perhaps the portion of the company Web site that is private. However, intranets use all of the inherent technologies characteristic of the Internet. For instance, within an intranet, TCP/IP protocols such as HTTP and FTP and email protocols like POP3 and SMTP are all employed just the same way as they are on the Internet. Again, the only difference is an intranet is a privatized version of the Internet, and any company can have one.
- An extranet is similar to an intranet except that it is extended to users outside a company, and possibly to entire organizations that are separate from or lateral to the company.
For instance, if a company often needs to do business with a specific organization, it might choose to set up an extranet in order to facilitate information sharing. User authentication is still necessary, and an extranet is not open to the general public.
The figure below illustrates both an intranet and extranet. Users can connect to intranets and extranets by simply logging in to a Web site or by using a virtual private network
Understanding Virtual Private Networks (VPN)
A VPN is a virtual private network that allows connectivity between two remote computers that are not part of the same private network. VPNs encrypt your internet traffic and disguise your online identity. This makes it more difficult for third parties to track your activities online and steal data. The encryption takes place in real time.

In order to ensure that only the proper users and data sessions cross to a VPN device, data encapsulation and encryption are used. A “tunnel” is created, so to speak, through the LANs and WANs that might intervene; this tunnel connects the two VPN devices together. Every time a new session is initiated, a new tunnel is created. Some technicians refer to this as tunneling through the Internet, although some VPN tunnels might go through private networks as well.
An illustration of a basic VPN is shown in figure below. Note that the VPN server is on one side of the cloud and the VPN client is on the other. The VPN client will have a standard IP address to connect to its own LAN. The IP address shown in the figure is the IP address it gets from the VPN server. The computer has two IP addresses; in essence, the VPN address is encapsulated within the logical IP address

How does a VPN work?
A VPN hides your IP address by letting the network redirect it through a specially configured remote server run by a VPN host. This means that if you surf online with a VPN, the VPN server becomes the source of your data. This means your Internet Service Provider (ISP) and other third parties cannot see which websites you visit or what data you send and receive online. A VPN works like a filter that turns all your data into “gibberish”. Even if someone were to get their hands on your data, it would be useless.
Types of VPNs
1. Remote Access VPNs/Client to Server VPN
A remote access VPN lets you use the internet to connect to a private network, such as your company’s office network.
The internet is an untrusted link in the communication. VPN encryption is used to keep the data private and secure as it travels to and from the private network.

To use a remote access VPN on your device you typically need to install client software or configure your device’s operating system to connect to the VPN. There also needs to be a VPN server on the network end of the connection.
Example: Somebody working from home could use a remote access VPN to access the company’s network from home. Their computer works as if it was connected to the company network in the office, and data is protected as it goes through the public internet.
2. Mobile VPNs
While remote access VPNs let you connect to a local network from anywhere, they do assume that the user will stay in one location. If the user disconnects, the IP tunnel closes.
A mobile VPN is a better option than a remote access VPN if the user is unlikely to have a stable connection, on the same network, for the entire session.
With a mobile VPN, the VPN connection persists even if the user switches WiFi or cellular network, loses connectivity, or switches their device off for a while. [Show diagram, for Mobile VPN]
Example: Professionals working from home in an area with poor connectivity could use a mobile VPN to maintain VPN access to the office all day, even when the connection is lost.
3. Site-to-Site VPNs
Whereas a remote access VPN is designed to let individual users connect to a network and use its resources, a site-to-site VPN joins together two networks on different sites.
If a company had two offices on the east coast and west coast, for example, a site-to-site VPN could be used to combine them into a single network. Site-to-site VPNs therefore enable organizations to combine their networks from different locations into a single network called an intranet

Site-to-Site VPN can be implemented by use of IPSec tunnelling or MPLS technology. Multi-Protocol Label Switched (MPLS) Layer 3-based VPNs can provide a guaranteed quality of service, with global connectivity. This is because MPLS is a way of routing packets across a network via any transport medium (such as fiber, satellite, or microwave) and any protocol.
When to Use a Site-to-Site VPN
- Intranet-Based VPN: When the networks being connected belong to a single company, the combined VPN is known as an intranet-based VPN. This enables a company to establish a single wide area network (WAN) that spans two or more of its offices. Users in the company can access resources from other sites as easily as if they were on their own site.
- Extranet-Based VPN: When the networks being connected belong to different companies, the combined VPN is known as an extranet-based VPN. An extranet VPN is used, for example, when a company wants to connect to its supplier’s network, so they can trade more efficiently.